Download Psiphon Pro MOD APK (Subscription Unlocked)

| Genres | Tools |
| Version | 366 |
| Developer | Psiphon Inc |
| Requires | 4.0 |
| Size | 31 MB |
| MOD Features | Subscription Features Unlocked |
| Updated | 2 days ago |
Section 1: Psiphon’s operation
Psiphon apk – Since 2006, Psiphon Inc. Has given millions of people access to the internet without restriction.
Both “Psiphon 2” and “Psiphon 3,” which are applications (“apps”) for android, windows, and iOS, are proxy systems run by Psiphon. The Psiphon 3 network, which is the most popular, is the subject of the following documents.
Psiphon is a censorship-bypassing program that is open-source and free. It enables users to connect with programs and material that would otherwise be prohibited by using a combination of secure communication and obfuscation technologies.
On the web
The internet is a massive, communicative network made up of billions of computers, or “routers.” people can exchange (or “serve”) information to others via these interconnected networks.
One way to think of the internet is a web with several links and paths. Due to the web infrastructure’s redundancy, users can still connect even if one connection is lost.
Web traffic, or messages delivered over the internet, must make numerous hops to go from one place to another. Before reaching its destination, traffic moves between routers.
Equipment for specific networking and routing is needed to accomplish this. Internet service providers (isps) offer this.
It typically charges consumers a fee for using its infrastructure, which includes “serving” content or giving access to content “served” by another isp.
Censorship and filtering
Filtering can occur at one or several places in the network, including the international gateway, isps, organizations (such as businesses or educational institutions), and even on a person’s device (such as a phone or desktop computer).
Censors are individuals who carry out filtering at any level. They might be filtering on behalf of a different organization, like when an isp censors information at the government’s behest.
First, it is necessary to identify the traffic to restrict blocking to specific types.
A system can decide what to do with certain types of traffic when it can distinguish between different types of traffic moving over the network.
Filtering can be carried out using tools and software that examine and prohibit the passage of specific types of traffic. Technical blocking can interfere with regular internet use in some locations.
Tools for circumvention
Psiphon apk belongs to the group of technological products known as circumvention tools. Tools for circumvention are made to get over interceptive technological online blocking.
Tools for circumvention often operate by either rerouting web traffic away from filtering devices or masking it to look like traffic not subject to filtering. The Psiphon app combines the two.
Because suppliers of circumvention tools are always updating their technology in response to the evolution of filtering techniques, tactics and strategies are also evolving.
Pioneer traffic
The Psiphon apk app’s main goal as a censorship-bypassing tool is to establish an internet connection. The Psiphon software makes several tries to connect to recognized Psiphon servers.
The Psiphon traffic may occasionally be obfuscated, which means that it is changed to look like another or less recognizable traffic.
Censors cannot view the content of traffic moving via the tunnel since it is encrypted. Despite encryption, censors may try blocking traffic based on other factors, such as communication protocols.
A set of guidelines called a communication protocol is used to route data and ensure it reaches its destination.Download Ibis Paint x Pro MOD APK (Prime Membership Unlocked).
The Psiphon app may relay traffic using several different communication protocols. Until a connection is formed, it tries to connect using various protocols.
In this manner, Psiphon can still connect even if a censor blocks one communication protocol by using another protocol.
It is crucial to make Psiphon’s communication appear as generic and typical to an outside observer as possible to ensure that it cannot be identified.
Even when specific information or traffic is censored, the Psiphon app can dynamically adapt to shifting network conditions by attempting multiple connection options.
What distinguishes Psiphon from a VPN?
Users can send and receive data through a secure network tunnel with the help of virtual private networks (VPNs).
Even though some VPNs use very strong encryption, most VPNs aren’t meant to be used for circumvention. VPNs are designed for typical network circumstances.
Vpn tools don’t take any particular measures to hide the nature of their traffic or stick to a single protocol for communication.
Since VPN communication can be recognized, censors can stop it. Many nations have been spotted filtering or throttling VPN connections, and others have been seen blocking VPNs in response to occasions like elections or political demonstrations.
Today’s censors can easily restrict this kind of content because of advances in censoring technology.
Users of the Psiphon apk can send and receive data via a secure network while hiding the nature of the transmitted traffic and its origin.
Psiphon technology is made to withstand censorship, including direct efforts to obstruct Psiphon network traffic.
Censors find it challenging to distinguish Psiphon traffic from other internet users because of the several secure protocols that Psiphon apps use.
Psiphon can connect through a different protocol even if a network filters a certain type of traffic. Where many other tools fail, Psiphon succeeds.
How do I know that Psiphon is reliable?
Because Psiphon is open-source software, anyone can inspect and comment on its source code to discuss how the system is constructed and the underlying cryptographic technologies.
Psiphon conducts internal code reviews and has frequent penetration testing and code audits carried out by various outside companies.
Section 2: Getting and installing Psiphon
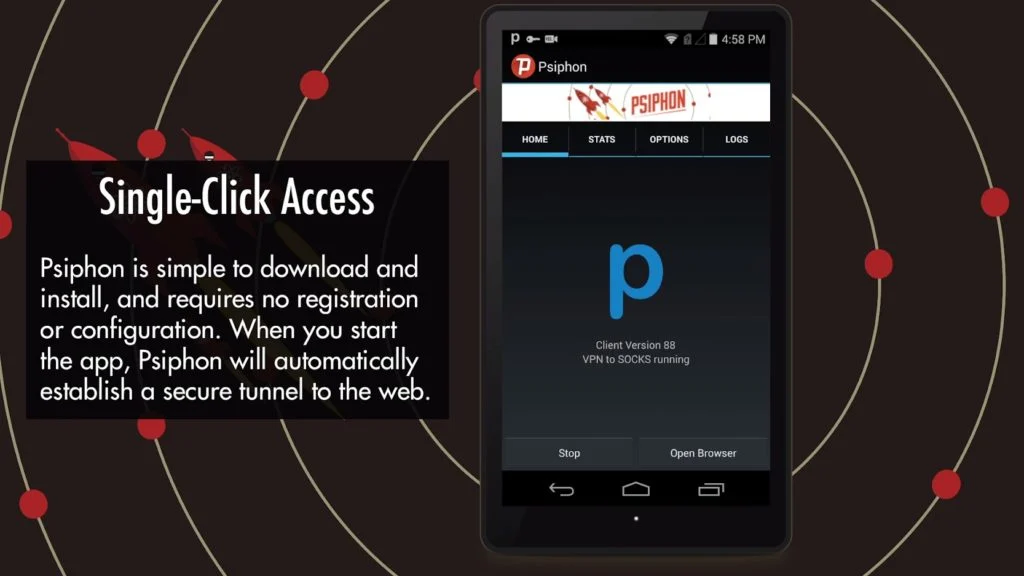
Multiple dissemination techniques are used to make Psiphon technology available. You can use alternative methods to download the software if one is blocked or unavailable in your country.
On our download page, Psiphon is available for android, iOS, and macs with apple silicon and windows.
Google play store on android: type “Psiphon” into the search bar. Depending on your region, you can download Psiphon pro with the option to subscribe. With this upgrade, you can speed up and get rid of advertising.
Installing the android email responder: you will soon receive an email from [email protected] in your inbox.
Check your spam folder if you don’t see it in your inbox. Visit the download URL or save the file ‘Psiphon android. ap_’ that is included in the email, then rename it if necessary to include the “.apk” file extension.
Install Psiphon. On your phone, locate the Psiphon icon, and click it to launch. Use a different email provider at the receiving address if you cannot receive the application immediately through the email responder.
Installing windows email responder: you will soon receive an email from [email protected] in your inbox. Check your spam folder if you don’t see it in your inbox.
Download the “psiphon3” file included in the email and rename it to end in “.exe.” use a different email provider at the receiving address if you cannot receive the application immediately through the email responder.
iOS: in the app store, type “Psiphon.” installation: to download and install Psiphon, conduct a search for it in the app store and select “get.” your apple id and password might need to be entered once again. On your phone, locate the Psiphon icon, and click it to launch.
Section 3: trust and security
Faith in the provider of a tool or service on the internet starts with trust in that company. The reliability of products and services can be evaluated using several key metrics.
The source code, sustainability approach, and external audits of the Psiphon apk are described in this publication.
Code of source
Psiphon is a project that is open source. Open source is software made available for public study and suggestion-making.
Open-source software can boost trust in the quality of application design by granting interested parties access to the source code.
Model for sustainability
Users have always had free access to Psiphon. Our goal is to reach as many individuals as possible, including breaking down barriers based on income.
Psiphon is dedicated to safeguarding the data of our users. So how does the business continue to operate a global network?
Psiphon can cover its operating expenses by continuing to receive revenue from a variety of sources, such as:
- Obtaining international subsidies for network upkeep and technology development.
- Employing branded Psiphon apk clients in collaboration with media partners to distribute content.
- Working together with ad networks in certain locations.
- Offering premium service subscriptions in specific areas.
A software audit is an internal or external assessment of a software program to assess its quality, development, standards, and security.
Regular internal code audits are conducted, and external code audits are typically initiated by significant code alterations like creating new functionality.
Audits of the source code’s external security are thorough evaluations by outside vendors to find and document flaws and dangers from outside sources. Psiphon users’ security is helped through audits.
Psiphon and the vendor will collaborate closely throughout the external code audit.
Any problems are dealt with according to importance by the vendor, who then retests the product. The public release of code reviews is a Psiphon policy.